
Transition to
Post Quantum
Cryptography (PQC)
TrustThink’s Cryptographic Architecture
and Trust Engineering Services
Plan your transition to post-quantum cryptography
Prepare your organization for emerging quantum-era security risks with practical post-quantum cryptography (PQC) strategy, crypto-agility engineering, and cryptographic modernization services.
TrustThink helps enterprises and government organizations identify cryptographic exposure, prioritize modernization efforts, and develop scalable migration roadmaps aligned with evolving standards and operational requirements.
From cryptographic discovery and risk assessment to hybrid cryptography adoption, PKI modernization, and secure architecture design, we help organizations transition toward quantum-resilient systems while maintaining interoperability and operational continuity.
Features & Benefits
Cryptographic Trust Architecture Design
Key and Certificate Management at Scale
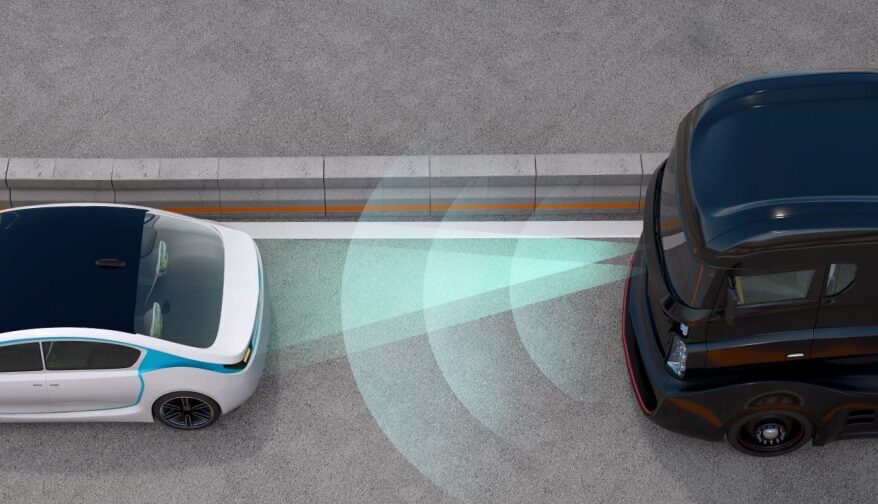
Secure Communications for Connected and Embedded Systems
SCMS and IEEE 1609.2 Certificate Integration
Preparing for Cryptographic Evolution
Cryptographic Trust Architecture Design
Effective cryptography begins with a clear trust model.
TrustThink supports the design and evaluation of cryptographic trust architectures that span devices, networks, applications, and operational environments. This includes:
Public Key Infrastructure (PKI) design and trust anchor strategy
Certificate lifecycle management and trust store design
Secure identity and authentication models
Encryption and signing for data in transit and at rest
We help organizations understand where trust decisions are made, how trust is established and revoked, and how cryptographic controls scale across complex systems of systems.
Key and Certificate Management at Scale
Strong cryptography depends on disciplined key and certificate management.
TrustThink helps organizations define and assess Key and Certificate Management Architectures (KCMA) that address:
Key generation, storage, rotation, and revocation
Secure handling of private keys, including HSM and TPM integration
Certificate issuance, renewal, and revocation workflows
Governance and operational procedures for managing trust over time

Our approach emphasizes operational realism—ensuring cryptographic controls can be managed reliably in production environments, not just specified in design documents.
Secure Communications for Connected and Embedded Systems
We have extensive experience integrating cryptography into resource-constrained, distributed, and safety-critical systems, including embedded platforms, mobile devices, and networked infrastructure.
This work includes:
Secure system-to-system communications
Authentication and authorization for distributed components
Root-of-trust design aligned with size, weight, and power constraints
Alignment with Zero Trust and least-privilege principles

TrustThink helps teams balance security, performance, and operational constraints while maintaining strong cryptographic assurance.
SCMS and IEEE 1609.2 Certificate Integration
TrustThink has deep experience with Security Credential Management Systems (SCMS) and IEEE 1609.2 certificates, supporting secure communications and trust establishment for connected transportation and mobility systems.
Our work includes:
Integrating SCMS-issued certificates into device and backend architectures
Designing certificate trust models and permissions handling
Supporting interoperability across jurisdictions and system owners
Aligning implementations with evolving standards and policy guidance

This experience directly informs our broader work designing certificate-based trust systems across other domains.
Preparing for Cryptographic Evolution
Cryptographic systems must be designed to evolve.
TrustThink helps organizations plan for long-term cryptographic change, including:
Post-quantum cryptography transition considerations
Algorithm agility and protocol evolution
Long-lived systems with extended security lifecycles
Interoperability across legacy and next-generation cryptographic solutions

We help teams understand not just what needs to change, but how to evolve cryptographic trust without disrupting mission or operations.
Explore Additional Services

AI Capability Maturity Model (CMM)

ITS Cybersecurity

Medical Device Cybersecurity & FDA Compliance

Cryptographic Key Management Systems

Autonomous & Robotic Systems Cybersecurity
Research, Development, & Prototyping
Learn more about TrustThink’s Cryptography
& Key Management services today
Whether establishing PKI foundations, integrating certificate-based trust at scale,
or preparing for cryptographic modernization, TrustThink helps organizations build trust that lasts.

