
Cybersecurity for Intelligent
Transportation Systems (ITS)
Enabling trust, interoperability, and secure operations
across connected transportation systems
TrustThink provides focused ITS cybersecurity services
that help organizations understand requirements,
reduce risk, and deploy systems with confidence.
Features & Benefits
Device Cybersecurity Assessments
Transportation Cybersecurity Standards and Guidance Development
Threat Modeling for Transportation Systems
Cybersecurity Training for Executives and Field Technicians
Device Cybersecurity
Assessments
Assess the cybersecurity posture of ITS devices, including RSUs, OBUs, traffic controllers, roadside sensors, and supporting infrastructure—against applicable standards and control sets. Assessments focus on configuration, credential use, software, interfaces, and lifecycle considerations to identify gaps that could impact deployment or certification.
Transportation Cybersecurity
Standards and Guidance
Development
Develop cybersecurity standards, control sets, and deployment guidance tailored to transportation environments. This includes aligning requirements with the ITS Cybersecurity Profile, NIST Cybersecurity Framework (CSF 2.0), and relevant IEEE, SAE, and ISO standards—written in a way that agencies and vendors can actually apply.

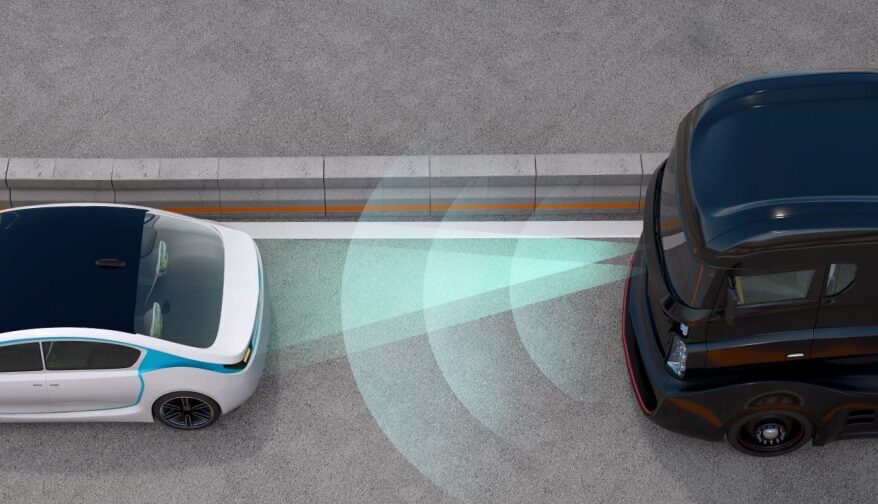
Threat Modeling for
Transportation Systems
Conduct threat modeling for connected transportation systems, devices, and applications to identify realistic attack scenarios, assess risk, and inform cybersecurity requirements. Our approach emphasizes operational relevance and supports architecture design, procurement language, and mitigation planning.

Cybersecurity Training for
Executives and Field Technicians
Develop and deliver role-based training that helps:
Executives and program leaders
understand cybersecurity responsibilities, risk tradeoffs, and governance decisions
Field technicians and implementers
apply cybersecurity requirements during installation, configuration, and maintenance

Grounded in Real-World Transportation Work
Our ITS cybersecurity services are informed by hands-on work supporting federal programs, state and local agencies, and industry stakeholders. This includes:
- Leading and contributing to transportation cybersecurity
standards and interoperability efforts - Developing ITS cybersecurity control sets and
implementation guidance - Supporting SCMS-related research, trust management approaches,
and misbehavior detection guidance - Aligning transportation cybersecurity practices with evolving national frameworks
- Translating standards into training and reference materials
used by practitioners

This experience allows us to anticipate the questions, constraints, and tradeoffs that agencies, vendors, and executives face, so our guidance is practical, defensible, and deployment-ready.
A Trusted System-of-Systems Perspective
TrustThink approaches ITS cybersecurity from a system-of-systems perspective. Connected transportation environments are not single products or standalone deployments—they are ecosystems of vehicles, roadside devices, applications, cloud services, and operators that must work together reliably over time.
In these environments, cybersecurity is less about securing one component and more about ensuring the entire system
can make consistent, defensible trust decisions as participants, policies, and technologies change.
This perspective shapes how we develop guidance, assess devices, model threats, and train stakeholders.
It also places trust at the center of ITS cybersecurity.
The Role of Trust in ITS Cybersecurity
At the heart of ITS cybersecurity is trust: the ability for devices, systems, and applications to reliably determine
who they are communicating with and whether that communication should be accepted.
Unlike traditional IT systems, ITS environments are:
Highly distributed
Operated across multiple organizations and jurisdictions
Deployed in public spaces for long lifecycles
Required to interoperate with equipment from many vendors
In this environment, cybersecurity is not just about protecting networks, it is about establishing and maintaining trust at scale.
Trust Enables Safe and Scalable Deployment
Managing Trust Across Jurisdictions and Vendors
Trust as a Foundation for the Future
Trust allows ITS components to:
- Authenticate other devices and applications
- Verify that messages and data have not been altered
- Ensure communications originate from authorized participants
- Enforce policy decisions across organizational boundaries
Without clear trust mechanisms, agencies and vendors face increased risk, interoperability challenges, and deployment delays.
As ITS deployments expand, trust must extend beyond a single agency or vendor.
Multi-jurisdictional and multi-vendor environments require:
- Clearly defined trust relationships and permissions
- Interoperability guidance that supports cross-boundary operations
- Alignment between policy, certificates, and operational behavior
TrustThink’s work in interoperability and standards development helps organizations navigate these challenges while maintaining security and flexibility.
Trust underpins emerging transportation capabilities, including:
- C-V2X deployments
- Cloud-based ITS services
- Virtualized and software-defined roadside systems
- AI-enabled transportation applications
By addressing trust early through architecture, standards, and guidance, organizations reduce downstream risk and enable systems that can scale over time.
Explore Additional Services

AI Capability Maturity Model (CMM)

ITS Cybersecurity

Medical Device Cybersecurity & FDA Compliance

Cryptographic Key Management Systems

Autonomous & Robotic Systems Cybersecurity
Research, Development, & Prototyping
Learn more about TrustThink’s
ITS Cybersecurity services today
Connect with our team to discuss how we can help secure your AI systems against adversarial threats

